Find Entra Service Principals Without Owners Using PowerShell
Service principals in Microsoft Entra ID represent applications, managed identities, and services that interact with your tenant. These identities often have permissions to access resources, APIs, and data.
However, service principals without assigned owners can pose a serious governance and security concern because:
- There is no accountability
- Permissions may go unmonitored
- They can become orphaned identities
- They increase the attack surface
👉 Identifying service principals with no owners is a critical step in strengthening your Entra security and governance posture.
This script helps administrators find service principals without any owners and export the results for auditing and remediation.
🚀 Community Edition Released!
Try the M365Corner Microsoft 365 Reporting Tool — your DIY pack with 20+ out-of-the-box M365 reports for Users, Groups, and Teams.
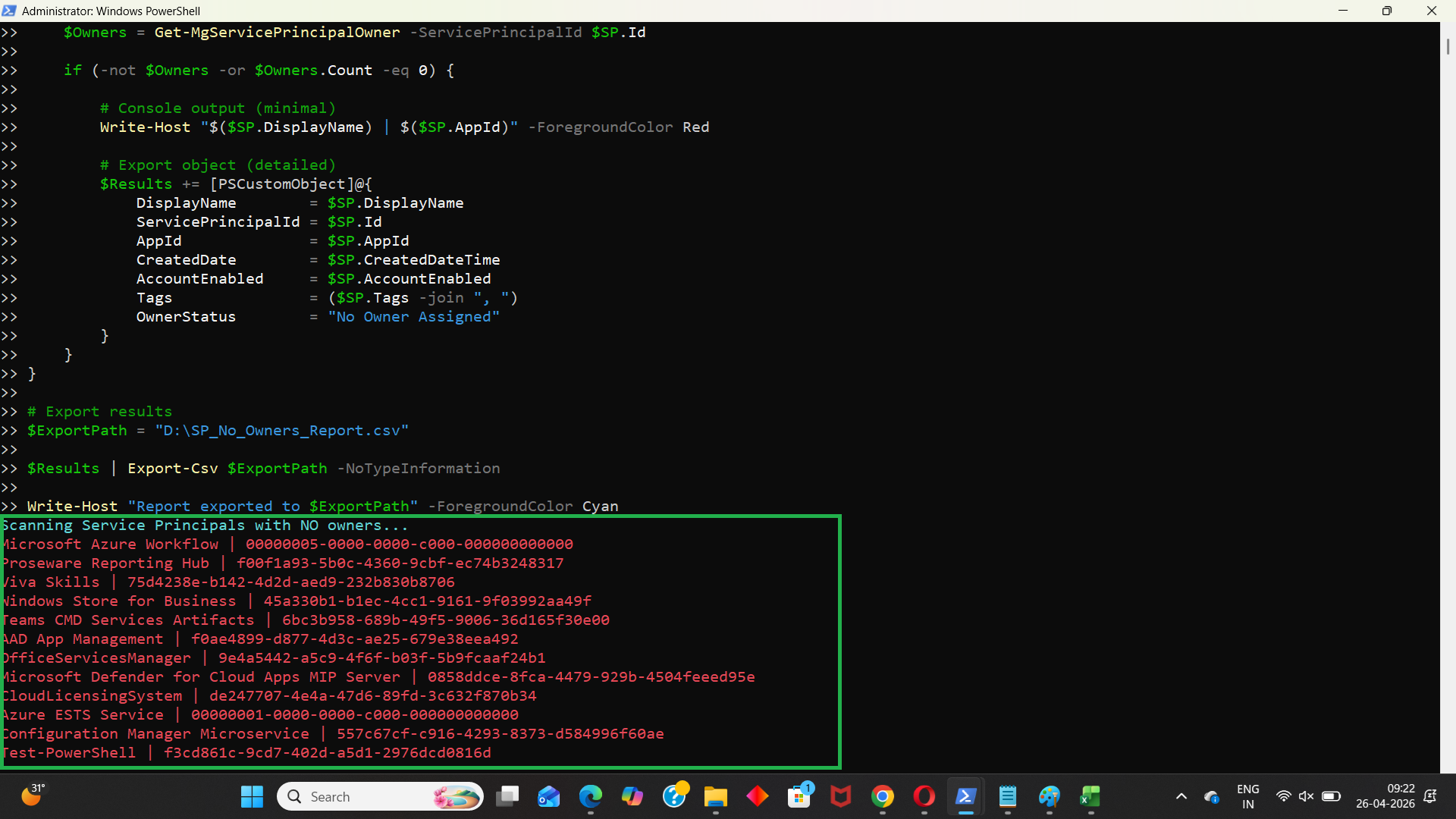
The Script
# Connect to Microsoft Graph
Connect-MgGraph -Scopes Application.Read.All, Directory.Read.All
Write-Host "Scanning Service Principals with NO owners..." -ForegroundColor Cyan
# Get all service principals
$ServicePrincipals = Get-MgServicePrincipal -All -Property Id,DisplayName,AppId,CreatedDateTime,AccountEnabled,Tags
$Results = @()
foreach ($SP in $ServicePrincipals) {
# Get owners
$Owners = Get-MgServicePrincipalOwner -ServicePrincipalId $SP.Id
if (-not $Owners -or $Owners.Count -eq 0) {
# Console output (minimal)
Write-Host "$($SP.DisplayName) | $($SP.AppId)" -ForegroundColor Red
# Export object (detailed)
$Results += [PSCustomObject]@{
DisplayName = $SP.DisplayName
ServicePrincipalId = $SP.Id
AppId = $SP.AppId
CreatedDate = $SP.CreatedDateTime
AccountEnabled = $SP.AccountEnabled
Tags = ($SP.Tags -join ", ")
OwnerStatus = "No Owner Assigned"
}
}
}
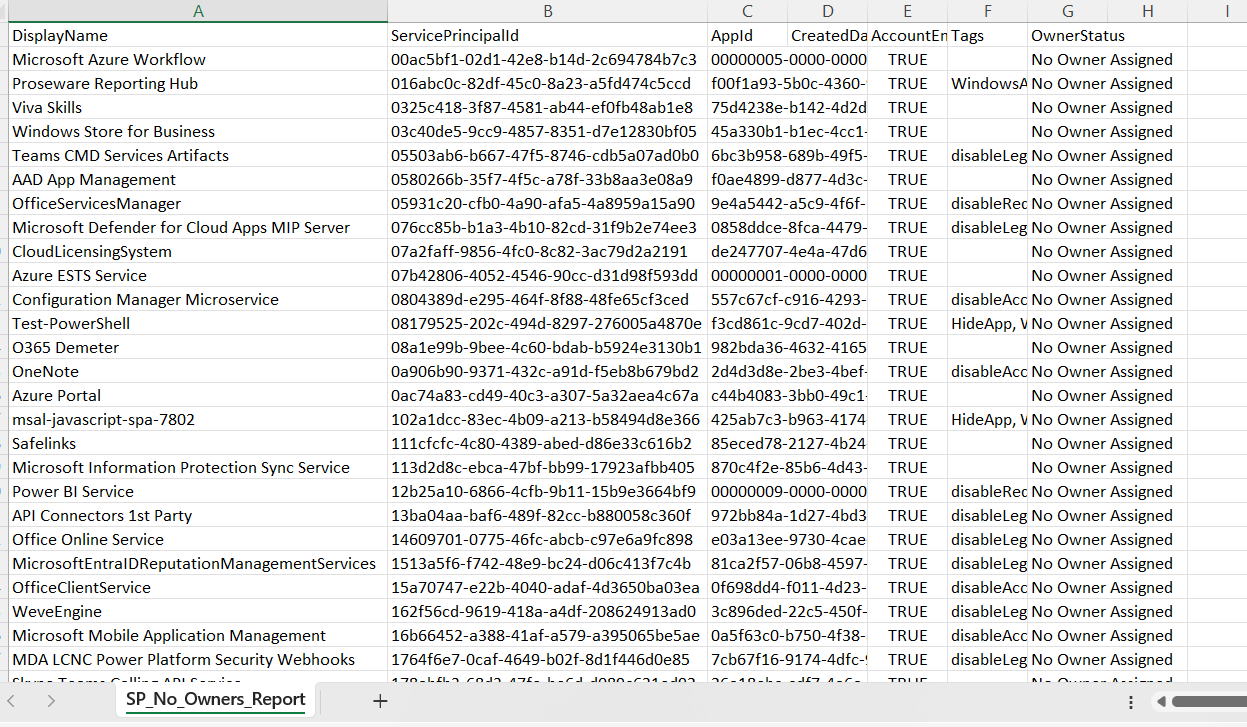
# Export results
$ExportPath = "D:\SP_No_Owners_Report.csv"
$Results | Export-Csv $ExportPath -NoTypeInformation
Write-Host "Report exported to $ExportPath" -ForegroundColor Cyan
How the Script Works
| Step | Description |
|---|---|
| Connect to Graph | Authenticates using Application.Read.All and Directory.Read.All |
| Fetch Service Principals | Retrieves all service principals using Get-MgServicePrincipal -All |
| Loop Through Each SP | Processes each service principal individually |
| Get Owners | Uses Get-MgServicePrincipalOwner to fetch assigned owners |
| Identify Orphaned SPs | Checks if owner list is empty or null |
| Build Report | Stores service principal details in structured format |
| Console Output | Displays orphaned service principals in real time |
| Export Results | Exports results to CSV for auditing |
Further Enhancements
| Enhancement | Description |
|---|---|
| Include Permissions | Add API permissions assigned to each service principal |
| Add Sign-In Activity | Identify inactive or unused service principals |
| Risk Classification | Tag orphaned service principals as medium/high risk |
| Include Application Type | Differentiate between app registrations and managed identities |
| Auto-Remediation | Assign owners or flag for review automatically |
Frequently Asked Questions
| Question | Answer |
|---|---|
| What is a service principal? | An identity used by applications or services in Entra ID |
| Why is ownership important? | Owners provide accountability and lifecycle management |
| Are ownerless service principals risky? | Yes, they can go unmanaged and pose security risks |
| Can service principals have multiple owners? | Yes, and this is recommended for critical apps |
| Should all ownerless SPs be deleted? | No, review usage before taking action |
Admin Usecases
| Use Case | Description |
|---|---|
| Security Audit | Identify unmanaged identities with access permissions |
| Governance Review | Ensure every service principal has an owner |
| Compliance Checks | Meet audit and regulatory requirements |
| Risk Management | Detect orphaned identities with potential access |
| Cleanup Activity | Remove or remediate unused service principals |
Possible Errors & Solutions
| Error | Cause | Solution |
|---|---|---|
| Insufficient privileges | Missing Graph permissions | Use Application.Read.All and Directory.Read.All |
| Cmdlet not recognized | Graph module not installed | Install using Install-Module Microsoft.Graph |
| Access token expired | Session timeout | Reconnect using Connect-MgGraph |
| Slow execution | Large number of service principals | Optimize with filtering |
| Null Tags property | Some SPs may not have tags | Add null handling if needed |
Conclusion
Service principals without owners represent a significant governance gap in Microsoft Entra ID environments. Without proper ownership, these identities can remain unmanaged, increasing security risks and reducing visibility.
This Microsoft Graph PowerShell script provides a practical way to identify service principals with no owners and generate a detailed report. By regularly auditing and addressing these orphaned identities, administrators can strengthen their security posture, improve governance, and ensure proper accountability.